 I’m not sure if cyber is a word that is used much outside the pages of a William Gibson novel or the Cyber security industry itself. It may not be many people’s vernacular yet it is a word that has come to dominate a lot of my time, both as an employ of the local authorities and now as a director of my own venture.
I’m not sure if cyber is a word that is used much outside the pages of a William Gibson novel or the Cyber security industry itself. It may not be many people’s vernacular yet it is a word that has come to dominate a lot of my time, both as an employ of the local authorities and now as a director of my own venture.
There has been a whole industry created to protect us and our technology assets ever since people realised that they could have a bit of fun or extort some money by fiddling round in our computers. Cybercrime has become a real threat and there are police departments up and down the country dedicated to catching the perpetrators and preventing future crimes. Don’t let anyone tell you that cyber is victimless though. Real people’s lives are turned upside down by it.
I hear different statistics bandied about. One set had it that 30% of CEOs of large organizations admitted to having had an attack of some sort, while another suggested that only 13% of SMEs were aware of having been hit. I imagine that the other 87% just don’t know they have been attacked already.
I had my eyes opened today though when I attended the Evolution of Cyber Security conference at the Core in Newcastle. It was sponsored by Invotra and was put on as part of the Digital Leaders’ cyber resilience week. There were some interesting speakers who told us through the advent of the threat and what is being done to protect us all. Let’s face it, it is an arms race out there, but the session that made me shiver the most was from a couple of guys from NCC.
For one of them, their job was to find ways of hacking into security features, breaking them that is, not to do anything unethical but rather to help the companies fix the problems. He showed us how to start cars, get into buildings, switch on people’s phones without them knowing and a whole host of other things that brought me out in a cold sweat.
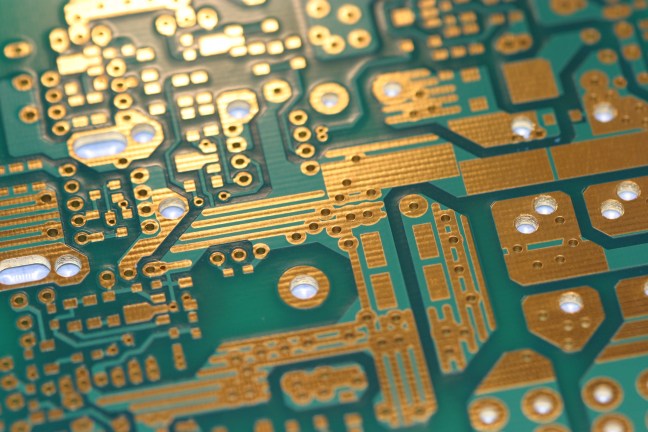
But what was most frightening was that this was all done at the hardware level. Unlike software, this cannot be fixed with a patch, or a rewrite. The threat or weakness is built into the physical structure of the kit. At best this will require rework or a retrofit. At worst you might as well chuck it away.
What he did was way above my technical ken, though that is not a very high bar, yet he showed that things are possible which I haven’t been aware of. He opened up a whole new front in the battle against cyber criminals. It’s terrifying to think what might happen.
As Andy Ward said, ‘In the Internet no one knows you are a toaster.’
